Cyber Coverage Recovery Framework™

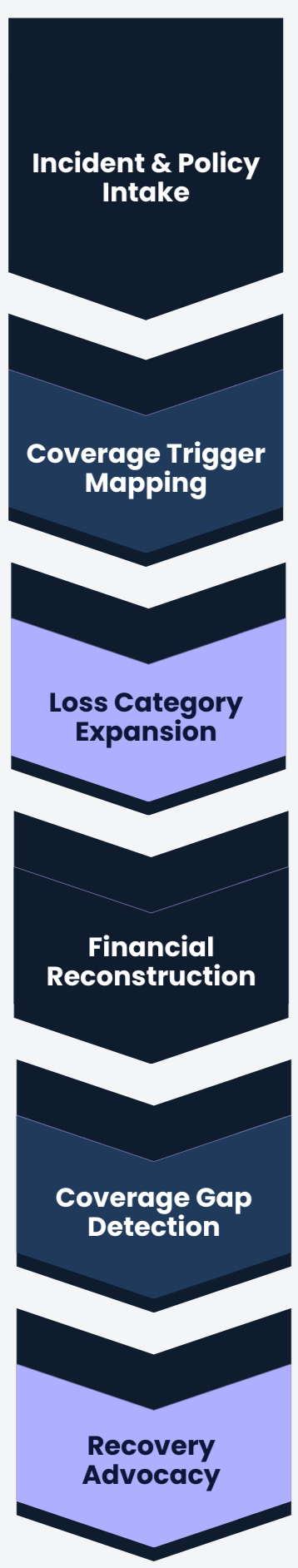
Phase 1 — Incident & Policy Intake
Objective
Establish factual foundation and confirm coverage structure.
Documents Required
Complete cyber insurance policy (all forms + endorsements)
Declarations page
Application submitted to carrier
Notice of claim submission
Carrier reservation of rights (if issued)
Incident timeline summary
Forensic engagement letter
What We Do
Review policy architecture
Identify coverage parts and sublimits
Evaluate potential misrepresentation exposure
Confirm claim reporting compliance
What the Client Should Expect
Structured document request
Clarification questions
Early identification of coverage strengths and risks
Determination of engagement viability
Phase 2 — Coverage Trigger Mapping
Objective
Align incident facts to policy triggers and coverage sections.
Documents Required
Forensic report (preliminary or final)
Ransom demand communications (if applicable)
System impact report
Downtime logs
Cloud / server impact summary
Carrier coverage correspondence
What We Do
Map incident mechanics to insuring agreements
Identify triggered coverage sections
Evaluate waiting periods
Identify applicable sublimits
Flag potential exclusions
What the Client Should Expect
Coverage pathway outline
Clear explanation of which sections respond
Identification of coverage expansion opportunities
Phase 3 — Loss Category Expansion
Objective
Identify all potentially covered loss categories beyond initial vendor invoices.
Documents Required
Vendor invoices (forensics, IR, legal, PR)
MSP billing statements
Internal IT labor allocation
Data restoration estimates
Third-party service interruption documentation
Regulatory notification costs
What We Do
Categorize expenses correctly
Identify overlooked cost buckets
Separate covered vs non-covered expense
Evaluate dependent system failure
Identify policy extensions
What the Client Should Expect
Reclassification of cost categories
Expanded loss matrix
Discovery of additional recoverable elements
Phase 4 — Financial Reconstruction
Objective
Quantify operational impact beyond vendor invoices.
Documents Required
Financial statements (12–24 months)
Revenue by product/service line
Sales pipeline data
Contracts with service level penalties
Payroll records
Cost of goods sold data
Business continuity reports
What We Do
Reconstruct business interruption period
Measure net income loss
Calculate continuing vs non-continuing expenses
Identify extra expense mitigation
Develop defensible financial model
What the Client Should Expect
Requests for financial data
Iterative clarification discussions
Preliminary BI valuation range
Clear explanation of methodology
Phase 5 — Coverage Gap Detection
Objective
Compare paid vs recoverable vs policy-available benefits.
Documents Required
Carrier payment summary
Proof of loss (if submitted)
Claim ledger
Adjuster reports
Carrier financial worksheets
What We Do
Perform paid-to-date reconciliation
Identify underpaid categories
Detect misapplied sublimits
Challenge improper waiting periods
Prepare recovery gap analysis
What the Client Should Expect
Gap report
Clear articulation of additional recoverable range
Strategy discussion before carrier engagement
Phase 6 — Recovery Advocacy
Objective
Pursue additional covered recovery in a structured, defensible manner.
Documents Required
Client authorization
Formal claim supplement package
Supporting schedules and matrices
Expert opinions (if needed)
What We Do
Present structured supplemental claim
Engage carrier adjusters
Negotiate recovery
Address carrier objections
Escalate where necessary
What the Client Should Expect
Controlled communication
Professional negotiation
Status updates
Resolution or structured escalation path
